There are 11 distinct types of ethical hacking, and most organizations only think about two or three of them. Everything outside that narrow band is a blind spot, and blind spots are where breaches happen. A colleague of mine once ran a quick social engineering test at a mid-sized firm, just a few phishing emails sent to internal staff as part of a sanctioned security review.
Within 20 minutes, two employees had entered credentials on a spoofed login page. No breach, no compromised data. But the gap was real, and it would have stayed invisible without the right type of test.

That’s the thing about ethical hacking: “types” can refer to what’s being hacked, how it’s being hacked, or who’s doing it. Each answer points to a different attack surface, a different set of tools and techniques, and a different level of exposure. Getting clear on all the various types is how you stop patching the obvious holes and start seeing the full picture.
But first, it helps to understand the three methodologies that cut across every one of them.
3 Methodologies of Ethical Hacking
Every type of ethical hacking, whether it’s web application hacking or social engineering, gets run through one of three methodologies. These are often called the “three boxes,” and they determine how much information the ethical hacker is given before an engagement starts.
That single variable changes the entire character of the test: the hacking techniques used, the attack surface covered, and how closely the simulation mirrors a real cyber threat.
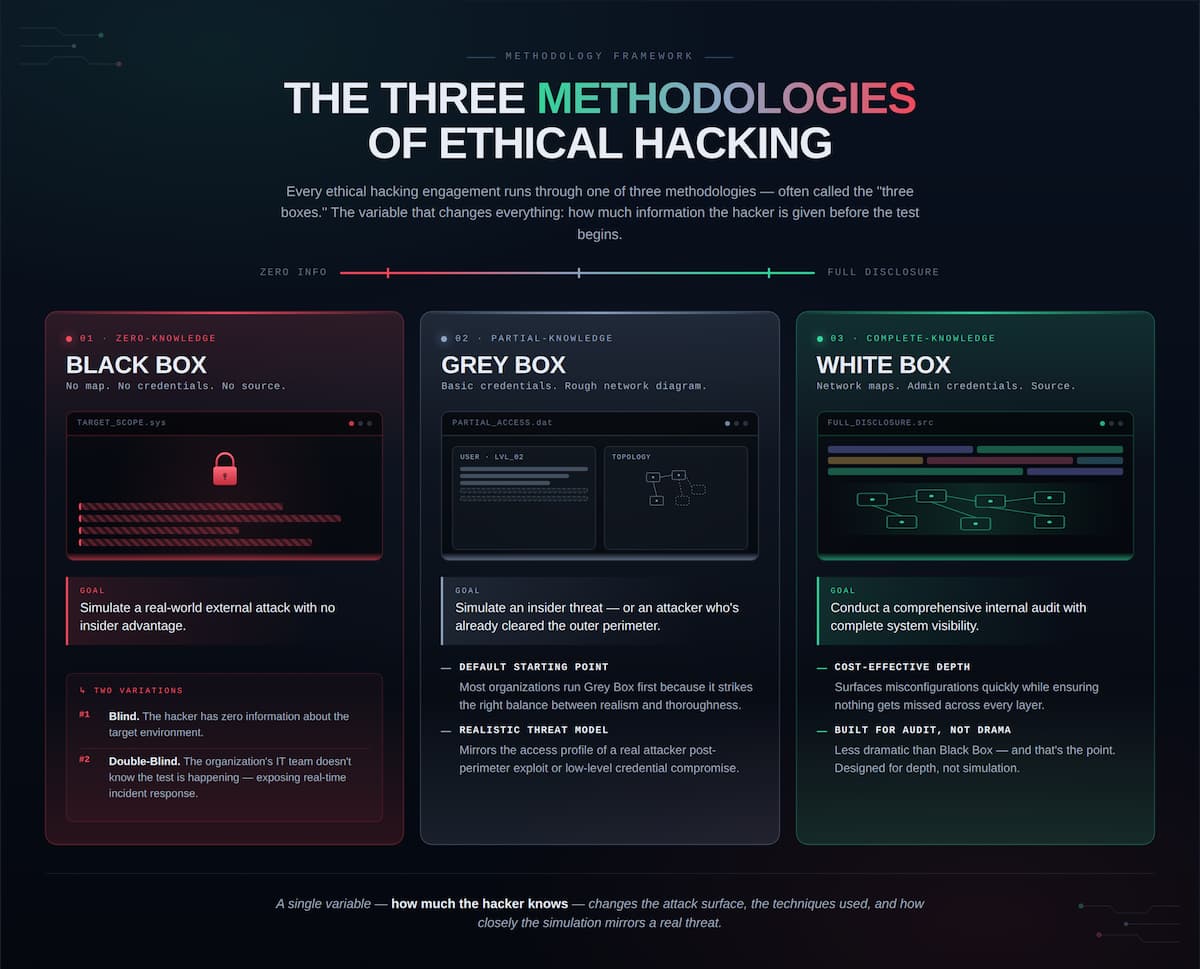
Black Box (Zero-Knowledge Testing)
In a Black Box test, the ethical hacker goes in with no prior knowledge of the target’s infrastructure or source code, which is exactly the position a malicious external attacker would be in.
- Goal: Simulate a real-world external attack with no insider advantage
- Variation #1 – Blind: The hacker has zero information about the target
- Variation #2 – Double-Blind: The organization’s own IT team doesn’t know the test is happening, exposing their real-time incident response
That last variation is uncomfortable for a lot of security teams. A security manager once told me his team had passed every previous penetration test with ease. Their first double-blind engagement revealed two critical vulnerabilities that went undetected for 36 hours… this is the kind of window that turns a security incident into a data breach headline.
White Box (Complete-Knowledge Testing)
The ethical hacker receives full transparency: network maps, administrative credentials, source code, all of it.
- Goal: Conduct a comprehensive internal audit with complete system visibility
- Key Benefit: Highly cost-effective for surfacing misconfigurations quickly while ensuring nothing gets missed
White Box tests are less dramatic than Black Box, but that’s the point. It’s designed for depth, not simulation. When the goal is to identify vulnerabilities across every layer of an internal system without leaving anything to chance, this is the methodology that delivers.
Grey Box (Partial-Knowledge Testing)
The hacker receives limited information, basic credentials or a rough network diagram, and works from there.
- Goal: Simulate an insider threat or an attacker who’s already cleared the outer perimeter
- Why it matters: That scenario is more common than most security teams want to admit
Grey Box testing is a deliberate middle ground, built to reflect the kind of access a real attacker might have after clearing an initial perimeter or exploiting a low-level account. Most organizations find that Grey Box strikes the right balance between realism and thoroughness, which is why it’s become the default starting point for a lot of security testing programs.
11 Types of Ethical Hacking
There are 11 types of ethical hacking across four categories, and most security programs don’t come close to covering all of them. From the outside, a regular penetration testing schedule looks like due diligence. The crack appears when you map what’s actually being tested against what isn’t. A strong security posture means nothing if your network goes untested, and neither protects you if an employee wires funds because they got a voicemail that sounded exactly like the CEO.
Types of ethical hacking:
- Network & Infrastructure Testing
- Wireless Network Testing
- IoT and OT Hacking
- Web and Mobile Application Testing
- Cloud Penetration Testing
- AI Security Testing
- Social Engineering Testing
- Physical Security Testing
- Insider Threat Testing
- Red Team Exercises
- Bug Bounty Programs

Group #1: Infrastructure & Connectivity
Network and Infrastructure Testing: Ethical hackers simulate attacks on routers, switches, and firewalls — scanning for open ports, misconfigured hardware, and anything a malicious attacker could use to gain access to internal systems. Network security failures are rarely dramatic. They’re usually a single overlooked configuration that’s been sitting there for months.
- Goal: Identify exploitable weaknesses across the core network layer before an attacker does.
- Common Targets: Routers, switches, firewalls, and network segmentation controls.
Wireless Network Testing: Testers use specialized tools to detect weak encryption standards, insecure configurations, and rogue access points — unauthorized devices quietly sitting on a network and intercepting traffic.
- Goal: Surface wireless vulnerabilities that fall outside standard network security scans.
- Watch for: Rogue access points introduced without IT knowledge, often by well-meaning employees.
IoT and OT Hacking: Smart devices and industrial control systems are among the most exposed targets in modern cybersecurity. Many were built without security measures as a core design consideration, making them easy entry points into much larger systems.
- Goal: Find and fix security gaps in devices that were never designed with security in mind.
- Why it matters: In operational technology environments, a breach can extend beyond sensitive data to physical infrastructure and, in serious cases, national security.
Group #2: Application & Cloud Security
Web and Mobile Application Testing: Ethical hackers analyze applications for software flaws like SQL Injection and Cross-Site Scripting vulnerabilities that allow an attacker to manipulate a system into doing something it shouldn’t. Application security failures drive a significant share of real-world breaches, largely because web applications are both complex and constantly changing.
- Goal: Identify code-level vulnerabilities before they become exploitable entry points.
- Common Flaws: SQL Injection, Cross-Site Scripting (XSS), broken authentication.
Cloud Penetration Testing: Cloud environments carry their own unique risk profile. Testing focuses on misconfigured APIs and identity and credential abuse, which accounts for roughly 35% of cloud-related security incidents.
- Goal: Assess the security of cloud platforms like AWS, Azure, and GCP against misconfigurations and credential-based attacks.
- Common Misconception: Moving to the cloud doesn’t automatically improve security, it shifts where the vulnerabilities live.
AI Security Testing: The newest frontier in ethical hacking, and one most security programs haven’t caught up to yet. One emerging threat is LLMJacking, where attackers exploit stolen credentials to access and resell enterprise machine learning models.
- Goal: Identify vulnerabilities specific to AI infrastructure and machine learning environments.
- Why it’s urgent: Most organizations running AI systems have no dedicated security testing protocol for them yet.
Group #3: The Human & Physical Element
Social Engineering Testing: The human firewall is still the most exploited vulnerability in cybersecurity. Ethical hackers now simulate attacks using GenAI-generated deepfakes to clone executive voices for vishing, also known as voice phishing, or craft hyper-convincing emails that bypass both filters and common sense.
- Goal: Evaluate how well staff can identify and resist manipulation-based cyber threats
- Modern Tactics: AI-generated deepfakes, voice cloning, hyper-personalized phishing emails
Physical Security Testing Not every breach starts at a keyboard. This type covers real-world controls: lockpicking, RFID badge cloning, and tailgating — following an employee through a secured door without authorization.
- Goal: Test whether physical security measures hold up against real-world intrusion attempts
- Common Gap: Organizations that invest heavily in digital security but leave physical access controls undertested
Insider Threat Testing: This type simulates scenarios where someone with existing privileges like a contractor, a disgruntled employee, or a compromised internal account, attempts to exfiltrate sensitive information.
- Goal: Determine how far legitimate access can reach before detection kicks in
- Why it’s hard: The attacker already has authorized access, which makes standard perimeter defenses irrelevant
Group #4: Advanced Adversarial Simulations
Red Team Exercises: Red teaming goes beyond standard penetration testing. A dedicated Red Team mimics the specific tactics, techniques, and procedures of real-world adversaries, actively trying to breach, move laterally, and achieve an objective while the organization’s defensive Blue Team tries to detect and stop them.
- Goal: Run a full-scale, realistic simulation of an actual attack to test detection and response capabilities
- Key Difference: Unlike standard security testing, Red Team exercises prioritize stealth and persistence over coverage
Bug Bounty Programs: Many organizations now run open bug bounty programs, inviting freelance ethical hackers to find and report vulnerabilities in exchange for rewards. It’s a crowdsourced approach to continuous security testing that keeps more eyes on the surface area year-round.
- Goal: Create a continuous, community-driven layer of vulnerability discovery outside of scheduled engagements
- Best used as: A complement to structured testing, not a replacement for it
Group #4: Advanced Adversarial Simulations
Red Team Exercises: Red teaming goes beyond standard penetration testing. A dedicated Red Team mimics the specific tactics, techniques, and procedures of real-world adversaries, actively trying to breach, move laterally, and achieve an objective while the organization’s defensive Blue Team tries to detect and stop them.
- Goal: Run a full-scale, realistic simulation of an actual attack to test detection and response capabilities
- Key Difference: Unlike standard security testing, Red Team exercises prioritize stealth and persistence over coverage
Bug Bounty Programs: Many organizations now run open bug bounty programs, inviting freelance ethical hackers to find and report vulnerabilities in exchange for rewards. It’s a crowdsourced approach to continuous security testing that keeps more eyes on the surface area year-round.
- Goal: Create a continuous, community-driven layer of vulnerability discovery outside of scheduled engagements
- Best used as: A complement to structured testing, not a replacement for it
Types of Ethical Hackers
The color of a hacker’s “hat” is the industry shorthand for something that actually matters: who has permission to do what, and what they intend to do with what they find. There are seven recognized types, and the line between them isn’t always as clean as it looks.
Hat color is a useful starting point, but it doesn’t tell the whole story. Understanding the types of ethical hacking, the methodologies behind them, and the people conducting the tests is what actually builds a security program worth trusting.
Tactical Phases: Types of Information Gathering and Scanning
To execute a successful engagement, professionals follow a strict technical workflow that begins with two foundational stages: Reconnaissance and Scanning. While it’s tempting to jump straight to exploitation, the quality of your initial intelligence usually dictates the success of the entire project
Phase 1: Reconnaissance (Footprinting)
Reconnaissance is the preparatory phase where you build a complete picture of the target’s environment, from IP ranges and DNS records to employee data. I’ve seen engagements stall simply because the initial footprinting missed a vital sub-domain or a legacy server. This intelligence gathering breaks down into two distinct approaches:
- Passive Reconnaissance: Collecting data without interacting with the target’s systems. Leaves no trace, carries no detection risk.
- OSINT: Mining public records for emails, phone numbers, and exposed credentials
- Social Media and Search Engines: Mapping employees for social engineering targeting or using Google Dorking to surface hidden files
- Public Registries: Querying WHOIS records for domain ownership details
- Active Reconnaissance: Directly engaging with the target for more detailed intelligence. More precise, but detectable.
- Network-Based Footprinting: Extracting usernames, shared resources, and network topology
- DNS Interrogation: Querying Domain Name Servers using tools like NSLookup
Phase 2: Types of Scanning and Enumeration
Once the footprint is established, the focus shifts to identifying the actual entry points: live systems, open ports, and vulnerable services. This is the “look but don’t touch” phase where you map the attack surface in high resolution.
- Network and Port Scanning: Mapping active machines and open ports using TCP Connect, SYN, and UDP scanning. Nmap and Wireshark are the standard tools here.
- Vulnerability Scanning: Automated tools like Nessus and OWASP ZAP check systems and web applications for known flaws across the network and application layers.
- Enumeration: The deepest layer. Goes beyond identifying live systems to extract usernames, group names, hostnames, routing tables, and application banners — the specific data that shapes the exploitation strategy.
Conclusion
Eleven types, three methodologies, seven hacker archetypes. The programs that hold up aren’t the ones that test the most often — they’re the ones that understand which tests they’re not running and why that matters.
Ready to build the skills behind the work? Our Ethical Hacking Bootcamp walks you through the methodologies, tools, and techniques used across every category covered in this guide, from reconnaissance to real-world operations.
Ethical Hacking FAQs
How can I practice these hacking types safely?
- TCM Security: Hands-on ethical hacking courses covering penetration testing, network security, and web application hacking
- New Horizons: Vendor-certified cybersecurity training with preparation for certifications like CEH and CompTIA Security+
What is the difference between a Red Team and a Blue Team?
Red Teams simulate attackers to breach systems and test stealth, while Blue Teams act as defenders to detect and contain threats. Many organizations now use Purple Team exercises, where both sides collaborate to improve overall response rather than competing.
Is Grey Hat hacking legal?
Generally, no. Intent doesn’t equal authorization, and unauthorized access is illegal in most jurisdictions regardless of motive. Grey hats face the same legal exposure as black hat hackers even when their intentions are benign. Good intentions don’t hold up well in court.
What skills and certifications are needed to become an ethical hacker?
You need a rock-solid grasp of networking (TCP/IP, DNS), Linux systems, and scripting (Python/SQL). While curiosity is the engine, these technical foundations are the fuel. Professionally, the industry typically looks for three key benchmarks:
- CompTIA Security+: The foundational entry point.
- Certified Ethical Hacker (CEH): A broad overview of tools and attack vectors.
- OSCP: The “gold standard” 24-hour hands-on exam for proving actual pentesting ability.
What are common tools used in ethical hacking?
An ethical hacker’s toolkit is specialized for each phase of an engagement. I’ve yet to see a professional environment that doesn’t rely on these essentials:
- Recon & Scanning: Nmap (network mapping) and Wireshark (packet analysis).
- Web Apps: Burp Suite or OWASP ZAP for intercepting traffic.
- Exploitation: Metasploit for executing exploit code.
- Vulnerability Assessment: Nessus for automated flaw detection.
- Password Cracking: John the Ripper or Hashcat.
Mastering these tools is a major milestone, but technical skill is only half the battle. It’s the “intent” behind the tool that defines the legal and professional boundaries of the work.
How does ethical hacking differ from penetration testing?
Ethical hacking is the broad “umbrella” discipline of using a hacker’s mindset to improve security, while a penetration test is a specific, time-bound project within that field. I’ve noticed people use these terms interchangeably, but a pentest is essentially a “point-in-time” check to find and exploit as many holes as possible in a set scope.

About the Author: Megan Percy
Megan Percy is the Senior Product Manager at TCM Security, where she focuses on building impactful cybersecurity training. With a background spanning digital forensics and network security, she’s passionate about making complex ideas accessible through great storytelling. When she’s not shaping the future of the TCMS platform, you’ll find her reading, cooking, or playing Magic: The Gathering (Commander).
About TCM Security
TCM Security is a veteran-owned, cybersecurity services and education company founded in Charlotte, NC. Our services division has the mission of protecting people, sensitive data, and systems. With decades of combined experience, thousands of hours of practice, and core values from our time in service, we use our skill set to secure your environment. The TCM Security Academy is an educational platform dedicated to providing affordable, top-notch cybersecurity training to our individual students and corporate clients including both self-paced and instructor-led online courses as well as custom training solutions. We also provide several vendor-agnostic, practical hands-on certification exams to ensure proven job-ready skills to prospective employers.
Pentest Services: https://tcm-sec.com/our-services/
Follow Us: Email List | LinkedIn | YouTube | Twitter | Facebook | Instagram | TikTok
Contact Us: sales@tcm-sec.com
See How We Can Secure Your Assets
Let’s talk about how TCM Security can solve your cybersecurity needs. Give us a call, send us an e-mail, or fill out the contact form below to get started.
 New Horizons
New Horizons
 Project Management Academy
Project Management Academy
 Six Sigma Online
Six Sigma Online
 TCM Security
TCM Security
 TRACOM
TRACOM
 Velopi
Velopi
 Watermark Learning
Watermark Learning
 Login
Login