Ethical hacking is the authorized practice of testing computer systems, networks, and applications to find vulnerabilities before malicious attackers do. What separates ethical hackers from their malicious counterparts isn’t the techniques they use, its permission. Every engagement is governed by legal agreements, including a Master Services Agreement and Rules of Engagement, that define exactly what can be tested, when, and by whom.
In practice, ethical hacking helps organizations by:
- Identifying vulnerabilities before attackers do
- Simulating real-world attacks in controlled environments
- Supporting regulatory compliance and security standards
- Strengthening overall cyber resilience
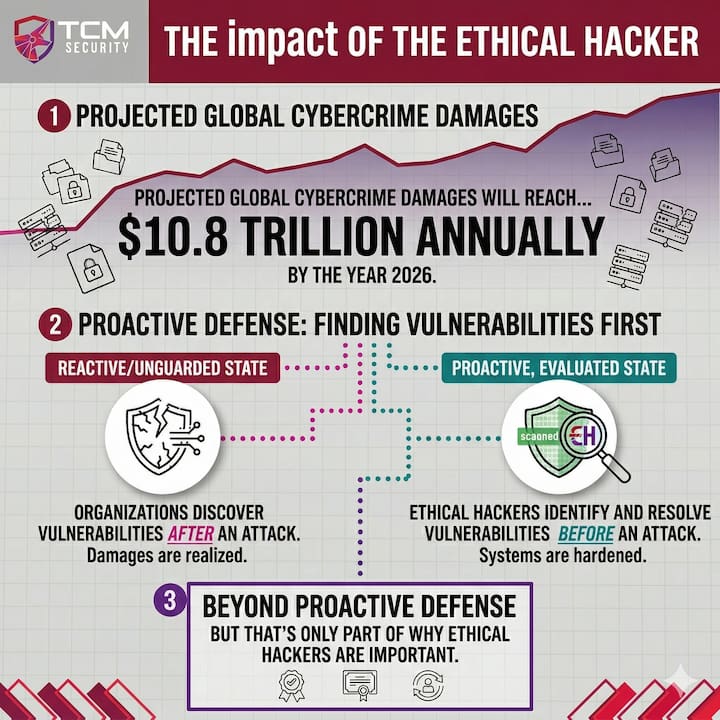
With global cybercrime damages projected to reach $10.8 trillion annually by 2026, ethical hacking gives organizations a proactive way to evaluate their defenses, before an attacker does it for them. But that’s only part of why ethical hackers are important.
Why is Ethical Hacking Important in Cybersecurity?
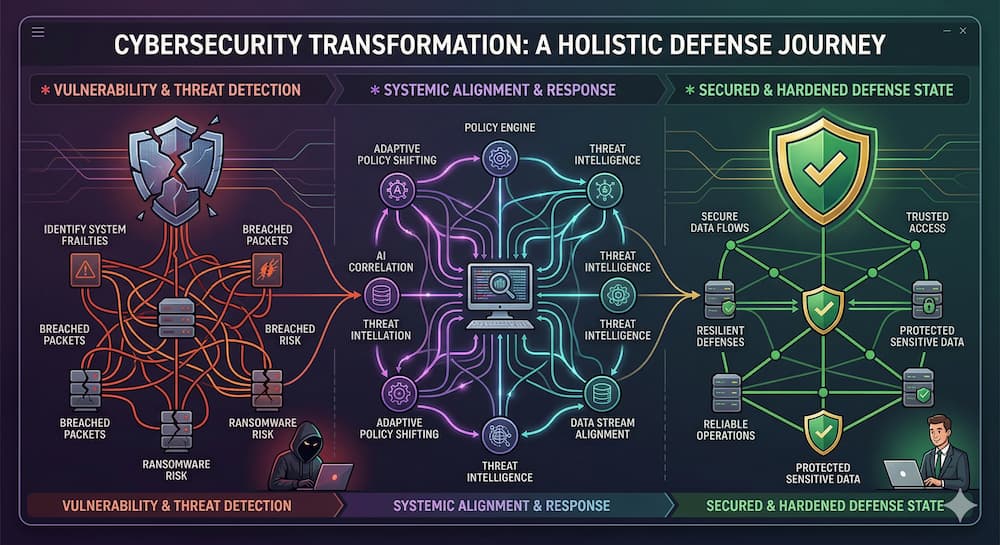
Security vulnerabilities exist in nearly every software system, network, and application. As organizations rely more heavily on digital infrastructure, identifying these weaknesses becomes critical for maintaining reliable operations and protecting sensitive data.
Programs that include regular security assessments provide organizations with a proactive way to evaluate defenses and uncover vulnerabilities. Ongoing testing improves visibility into system weaknesses, supports regulatory compliance, and helps teams prioritize security improvements.
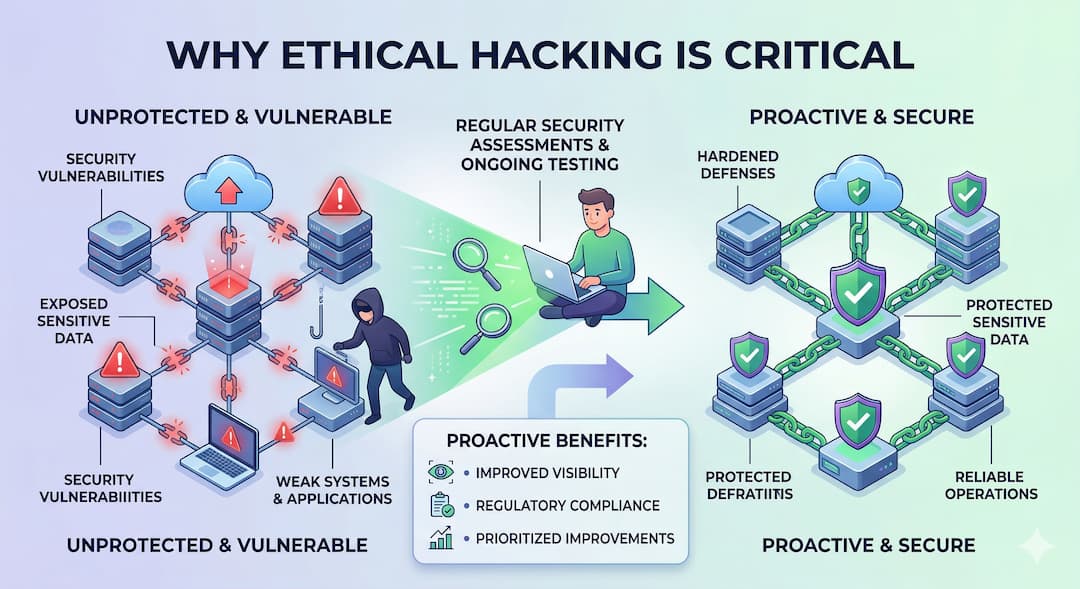
Proactive security testing provides several important benefits for organizations.
Key Benefits of Ethical Hacking:
- Vulnerability identification: Discovering security weaknesses before attackers do
- Risk reduction: Resolving vulnerabilities before exploitation occurs
- Infrastructure protection: Securing networks, applications, and systems
- Regulatory compliance: Supporting security testing requirements
- Security resilience: Strengthening defenses against evolving threats
These benefits give organizations greater visibility into their security posture. Defensive tools alone cannot detect every potential vulnerability. An ethical hacking program enables security teams to actively identify weaknesses and address them before they lead to security incidents.
Within broader cybersecurity strategies, ethical hacking serves as an important evaluation method. Organizations use multiple security assessment techniques to test system defenses and validate vulnerabilities.
History of Ethical Hacking
The roots of ethical hacking trace back further than most people expect. In the 1940s and 50s, MIT students were already probing system boundaries out of pure curiosity, treating computers as puzzles to be solved rather than tools to be feared. That spirit carried into the phone phreaking movement of the 1960s and 70s, where hobbyists, including a young Steve Wozniak and Steve Jobs, exploited the global telephone network for sport. Understanding how systems break, it turned out, was the first step toward securing them.
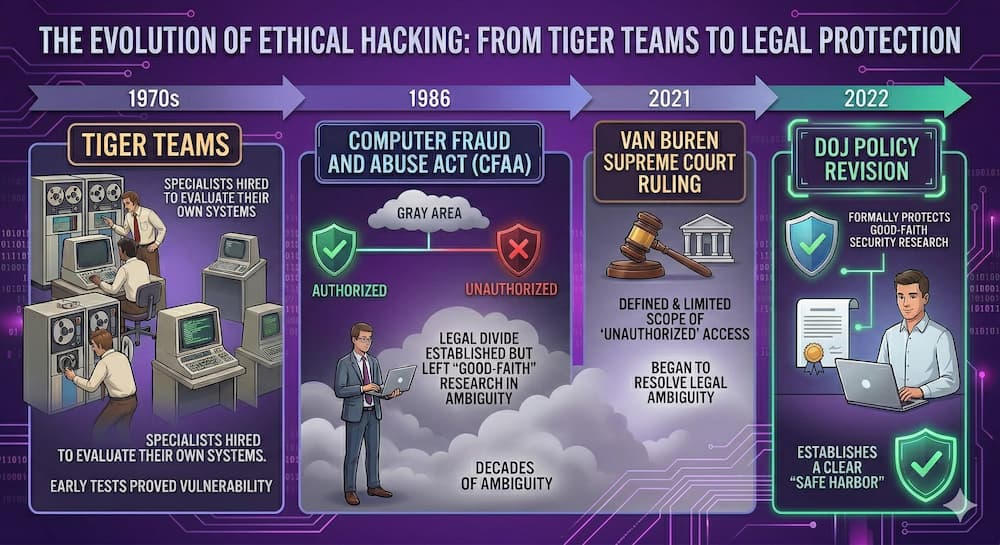
By the 1970s, the U.S. Department of Defense was organizing “Tiger Teams,” specialists hired to break into their own systems, and early results were humbling. Almost everything they tested could be penetrated. The 1986 Computer Fraud and Abuse Act drew a legal line between authorized and unauthorized access, though it left good-faith researchers in a gray area for decades. That ambiguity wasn’t resolved until the Supreme Court’s 2021 Van Buren ruling and a 2022 DOJ policy revision formally protected good-faith security research.
Key milestones in the discipline’s evolution:
- 1946: MIT’s Tech Model Railroad Club coins the term “hack” to describe clever technical problem-solving
- 1970: The Willis Report formally validates Tiger Teams as a legitimate security practice
- 1986: The Computer Fraud and Abuse Act criminalizes unauthorized access, separating ethical from malicious hacking
- 1995: IBM’s John Patrick coins “ethical hacking”; Netscape launches the first bug bounty program
- 2003: The EC-Council launches the CEH certification, formalizing ethical hacking as a recognized profession
- 2021: The Supreme Court’s Van Buren ruling provides legal protections for good-faith security researchers
- 2022: The DOJ revises its CFAA charging policy, formally directing for the first time that good-faith security research should not be prosecuted as a federal crime
Companies like TCM Security, founded in 2019 with a mission to make practical, affordable cybersecurity training accessible to everyone, reflect how far the industry has come. What began in academic labs and government corridors now reaches the next generation of security professionals worldwide, equipping them with the hands-on skills needed to stay ahead of an ever-evolving threat landscape.
Principles of Ethical Hacking
Ethical hacking is guided by a clear set of principles designed to improve security without causing harm. These principles are what separate a trusted security professional from a malicious actor — and what make ethical hacking a legitimate, valuable discipline rather than simply unauthorized intrusion with good intentions.
- Authorization and Permission: No testing begins without explicit, written consent from the system owner. This protects both parties legally and ensures all activities are conducted within a sanctioned framework.
- Scope and Objectives: Ethical hackers define and operate within agreed boundaries, specifying exactly which systems, networks, and applications are in scope. A clearly defined scope prevents unintended disruptions and keeps the engagement aligned with the organization’s security goals.
- Confidentiality and Privacy: All sensitive data encountered during testing is handled with strict confidentiality. Ethical hackers routinely sign non-disclosure agreements and are responsible for ensuring that discovered information does not leave the engagement improperly.
- Integrity and Professionalism: Ethical hackers maintain high standards of honesty and accountability in every interaction. Professional conduct builds the trust that organizations need to feel comfortable granting access to their most sensitive systems.
- Reporting and Disclosure: Every vulnerability discovered must be thoroughly documented and reported, along with clear recommendations for remediation. The value of an ethical hacking engagement is ultimately measured by the quality and clarity of its findings.
- Do No Harm: Tests must be designed to avoid damaging systems, interrupting services, or resulting in data loss. Ethical hacking is about identifying risk, not creating it.
5 Phases of Ethical Hacking
Ethical hacking follows a structured, five-phase methodology designed to identify and exploit system vulnerabilities in a controlled, legal manner. Each phase builds on the last, allowing security professionals to move methodically from information gathering to a final report that organizations can act on. Skipping or rushing any phase risks missing critical vulnerabilities that a real attacker would not overlook.
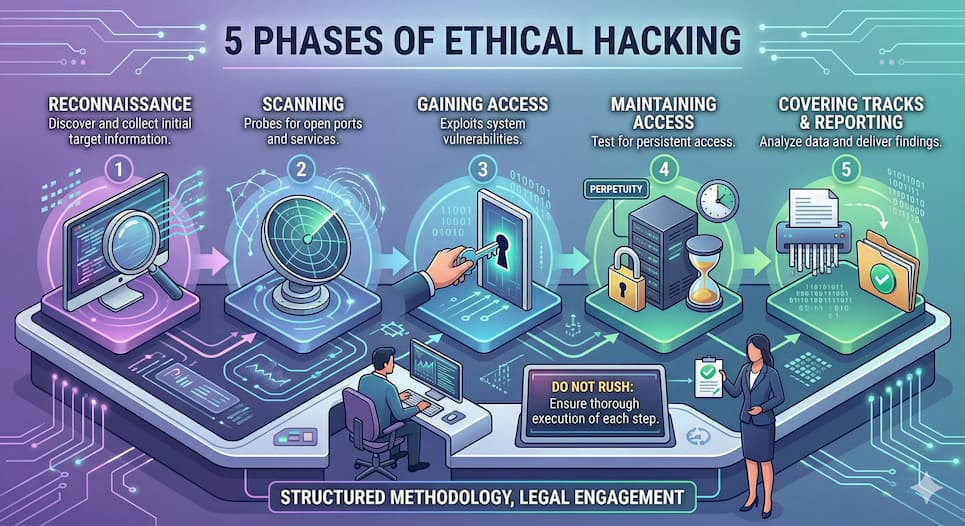
Phase 1: Reconnaissance
Reconnaissance is the foundation of every ethical hacking engagement. Before any testing begins, the ethical hacker gathers as much information as possible about the target system or organization to plan an effective approach.
- Passive reconnaissance: Collecting information without directly interacting with the target, such as searching public records, LinkedIn, social media, and other open sources.
- Active reconnaissance: Directly engaging with the target system through techniques like port scanning and network enumeration to build a more detailed picture of potential vulnerabilities.
Phase 2: Scanning
With reconnaissance complete, the ethical hacker uses specialized tools to probe the target network for open ports, active hosts, and exploitable weaknesses. This phase transforms general information into specific, actionable targets.
- Common tools include Nmap for port scanning, Nessus for vulnerability detection, and Wireshark for analyzing network traffic.
- Open ports are flagged as potential entry points and prioritized for the next phase.
Phase 3: Gaining Access
This is the exploitation phase, where the ethical hacker attempts to access the target system by leveraging the vulnerabilities identified during scanning. It is the most technically demanding phase and requires careful execution to avoid disrupting live systems.
- Common methods include SQL injection, phishing, social engineering, and exploiting unpatched software vulnerabilities.
- Tools like Metasploit are commonly used to simulate real-world attacks in a controlled manner.
Phase 4: Maintaining Access
Once access is gained, the ethical hacker tests whether that access can be sustained over time, simulating the behavior of a real attacker who wants to remain inside a system undetected.
- Techniques include installing backdoors, deploying rootkits, and creating new user accounts to test the persistence of the vulnerability.
- This phase helps organizations understand the full potential impact of a successful breach, not just the initial point of entry.
Phase 5: Covering Tracks and Reporting
The final phase serves two purposes: simulating how a real attacker would attempt to hide their presence, and delivering a structured report the organization can act on.
- Covering tracks involves deleting logs, clearing temporary files, and removing tools used during the assessment.
- The report documents all identified vulnerabilities, evidence of access, risk assessments, and prioritized remediation recommendations to help the organization strengthen its defenses.
Types of Hackers in Cybersecurity
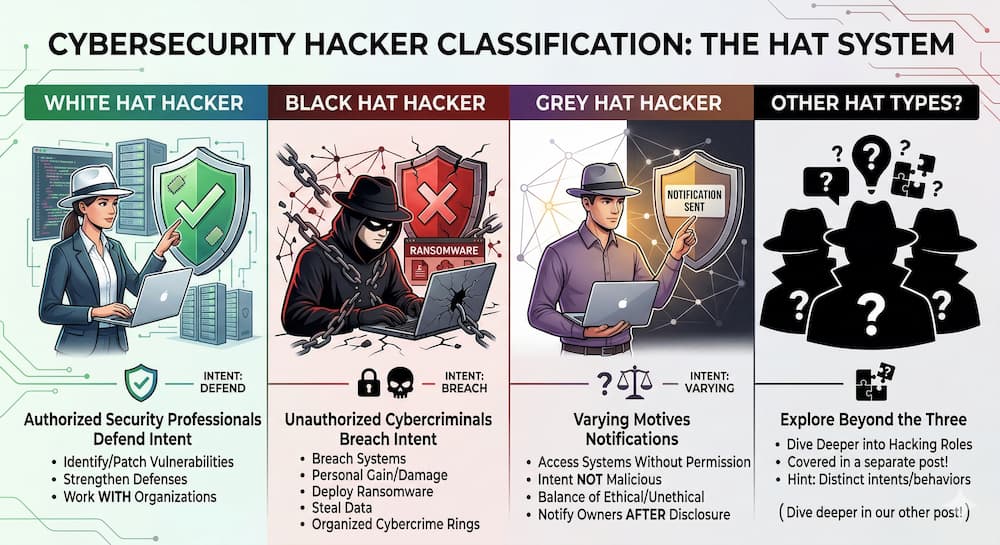
Cybersecurity professionals often classify hackers using a “hat” system that describes their intent and behavior. These labels help explain whether someone is working to improve security, exploit vulnerabilities for personal gain, or operate somewhere in between.
3 Types of Hackers:
- White hat hackers: Authorized security professionals who identify and patch vulnerabilities to strengthen defenses. They work with organizations to secure systems against potential attacks.
- Black hat hackers: Cybercriminals who breach systems for personal gain or to cause damage, often deploying ransomware, stealing data, or operating within organized cybercrime rings.
- Grey hat hackers: Individuals who may access systems without permission but not always with malicious intent, sometimes notifying owners of discovered vulnerabilities after the fact.
These three categories cover most of the landscape, but there are more specialized types worth understanding including hacktivists, red hat hackers, and insider threats. Our complete guide on Types of Ethical Hacking breaks each one down in detail.
What Do Ethical Hackers Do?
Security professionals performing ethical hacking conduct structured assessments designed to evaluate how organizations protect their systems and data. Their responsibilities span the full engagement lifecycle, from initial scoping and reconnaissance through exploitation, documentation, and remediation support.
What surprises many people is how the time actually breaks down in practice. Manual hacking, the part most commonly depicted in media, accounts for roughly 5% of a typical work week. The majority of the role looks more like this:
- Documentation and reporting (30%): Meticulously documenting every command, output, and screenshot to prove the existence of each vulnerability.
- Threat hunting and exploit creation (20-50%): Manual enumeration, custom script development, and bypassing defenses.
- Meetings and stakeholder management (5-20%): Translating technical findings into language that resonates with both engineers and executives.
- Planning and scoping (10%): Ensuring all testing stays within the legal and ethical boundaries of the engagement.
Reporting alone accounts for roughly 30% of an engagement. Every command entered, every vulnerability discovered, and every piece of evidence collected must be documented with enough clarity that both technical teams and executive leadership can act on the findings.
Key Skills for Ethical Hackers
Technical skills form the foundation, but the most effective ethical hackers combine them with strong analytical and communication abilities.
Technical Skills:
- Networking fundamentals: Deep understanding of TCP/IP, DNS, HTTP/S, and the OSI model
- Operating systems: Proficiency in Linux and Windows, including Active Directory environments
- Scripting and automation: Ability to write Python or Bash scripts for reconnaissance and custom exploits
- Security tools: Hands-on experience with tools like Nmap, Burp Suite, Wireshark, and Metasploit
- Vulnerability assessment: Identifying, validating, and prioritizing security weaknesses across systems and applications
Soft Skills:
- Communication: Translating complex technical findings into clear, actionable guidance for both technical and non-technical audiences
- Analytical thinking: Approaching systems from an attacker’s perspective to identify unconventional attack paths
- Attention to detail: Meticulously documenting findings, evidence, and methodologies throughout every engagement
- Integrity and professionalism: Operating within strict legal and ethical boundaries at all times
“Finding vulnerabilities is only part of the job.” Aaron Wilson, Red Team Lead at TCM Security, emphasizes that communication is just as important as technical skill. “Ethical hackers must explain problems clearly and help organizations understand how to fix them.”
One often-overlooked benefit of offensive security roles is work-life balance. Unlike defensive blue team roles, where professionals may be on-call around the clock, red teamers and penetration testers typically work scheduled engagements during standard business hours, making it one of the more sustainable career paths in cybersecurity.
How Much Do Ethical Hackers Make?
Ethical hacking is one of the more lucrative career paths in cybersecurity, with compensation that scales significantly with experience and specialization. In the United States, the average salary ranges from $95,000 to $120,000, though that number moves considerably depending on experience level and industry.
Experience-Based Salary Ranges (U.S.):
- Entry-level (0-2 years): $65,000 – $85,000
- Mid-level (3-7 years): $85,000 – $140,000
- Senior level (8+ years): $140,000 – $250,000+
- Expert/independent consulting: $200,000 – $500,000+
Certifications also play a tangible role in compensation. CEH and PNPT certifications can add $10,000 to $20,000 to an annual salary by demonstrating practical, hands-on technical ability. Industry also matters: professionals working in financial services or healthcare can expect to earn 15% to 40% above market average due to the complexity of regulatory environments like PCI-DSS and HIPAA.
For a deeper look at how to enter the field and build toward these salary ranges, check out our full guide on How to Become an Ethical Hacker.
Job Growth and Emerging Areas in Ethical Hacking
Demand for ethical hackers continues to outpace supply, with the global cybersecurity talent gap reaching 4.8 million unfilled positions according to the 2025 ISC2 Cybersecurity Workforce Study, with the workforce needing to grow 87% to satisfy current demand.
Hakia Job growth for information security analysts tells a similar story, the U.S. Bureau of Labor Statistics projects 29% growth from 2024 to 2034, much faster than the average for all occupations, with approximately 16,000 new openings projected each year over the decade.
As organizations adopt new technologies, the environments requiring security testing continue to expand. Cloud platforms, connected devices, and artificial intelligence systems create new attack surfaces that ethical hackers must evaluate to help secure modern digital infrastructure.
Several growing areas are shaping the future of ethical hacking.
Key Emerging Areas in Ethical Hacking:
- Internet of Things (IoT) security: Testing connected devices and embedded systems
- Cloud infrastructure security: Assessing security controls in cloud platforms and services
- Artificial intelligence security: Evaluating vulnerabilities in AI models and machine learning systems
These emerging areas introduce new attack surfaces that require specialized testing methods. Organizations adopting new technologies must evaluate the security implications those systems create. As these technologies evolve, organizations increasingly rely on specialized security testing skills to identify and address emerging vulnerabilities.
Getting Started With Ethical Hacking
Ethical hacking has become an essential part of modern cybersecurity strategy, and getting started is more accessible than ever. New Horizons offers foundational courses including CompTIA Security+, CompTIA PenTest+, and the EC-Council Certified Ethical Hacker (CEH) to help learners build core knowledge in vulnerability assessment and security operations.
For those ready to develop hands-on offensive security skills, TCM Security’s training programs are built around the realities of professional penetration testing. The PJPT is the ideal starting point for beginners, while the PNPT is designed for those ready to prove their skills at an advanced level. Explore TCM Security’s training programs to get started.
Explore TCM Security’s training programs to begin building the hands-on skills used by professional ethical hackers and penetration testers.
Frequently Asked Questions
Where Can Beginners Learn Ethical Hacking Skills?
Beginners can learn ethical hacking through structured cybersecurity training programs and hands-on lab environments.
Recommended learning providers include:
These providers offer cybersecurity courses and practical labs that help learners build real-world security skills.
What Is The Salary Of An Ethical Hacker?
According to the U.S. Bureau of Labor Statistics, the median annual salary for information security analysts is $120,360. Employment in this field is projected to grow 29 percent from 2024 to 2034, much faster than the average for most occupations.
When Is Ethical Hacking Legal?
With the system owner’s authorization, ethical hacking is legal and conducted within an approved scope of testing. Security professionals operate under defined rules of engagement and legal agreements that establish the scope of testing. Attempting to access systems without permission may constitute a computer crime.
What Is the Purpose of Ethical Hacking?
The purpose of ethical hacking is to evaluate the effectiveness of an organization’s cybersecurity defenses. Authorized security assessments help identify vulnerabilities, understand potential attack paths, and guide remediation efforts that improve overall system security.
What Tools Are Commonly Used in Ethical Hacking?
Ethical hackers use specialized cybersecurity tools to identify vulnerabilities and evaluate system security. Common examples include network scanners, vulnerability assessment platforms, and web application testing tools used during security assessments.

About the Author: Andrew Bellini
My name is Andrew Bellini and I sometimes go as DigitalAndrew on social media. I’m an electrical engineer by trade with a bachelor’s degree in electrical engineering and am a licensed Professional Engineer (P. Eng) in Ontario, Canada. While my background and the majority of my career has been in electrical engineering, I am also an avid and passionate ethical hacker.
I am the instructor of our Beginner’s Guide to IoT and Hardware Hacking, Practical Help Desk, and Assembly 101 courses and I also created the Practical IoT Pentest Associate (PIPA) and Practical Help Desk Associate (PHDA) certifications.
In addition to my love for all things ethical hacking, cybersecurity, CTFs and tech I also am a dad, play guitar and am passionate about the outdoors and fishing.
About TCM Security
TCM Security is a veteran-owned, cybersecurity services and education company founded in Charlotte, NC. Our services division has the mission of protecting people, sensitive data, and systems. With decades of combined experience, thousands of hours of practice, and core values from our time in service, we use our skill set to secure your environment. The TCM Security Academy is an educational platform dedicated to providing affordable, top-notch cybersecurity training to our individual students and corporate clients including both self-paced and instructor-led online courses as well as custom training solutions. We also provide several vendor-agnostic, practical hands-on certification exams to ensure proven job-ready skills to prospective employers.
Pentest Services: https://tcm-sec.com/our-services/
Follow Us: Email List | LinkedIn | YouTube | Twitter | Facebook | Instagram | TikTok
Contact Us: sales@tcm-sec.com
See How We Can Secure Your Assets
Let’s talk about how TCM Security can solve your cybersecurity needs. Give us a call, send us an e-mail, or fill out the contact form below to get started.
 New Horizons
New Horizons
 Project Management Academy
Project Management Academy
 Six Sigma Online
Six Sigma Online
 TCM Security
TCM Security
 TRACOM
TRACOM
 Velopi
Velopi
 Watermark Learning
Watermark Learning
 Login
Login